Privacy focused art show in Plano Texas
I recently received a press release that intrigued me and though might interest you. There is going to be a multi-media art installation focused on modern privacy risks that looks like it could be fun. Here is the release:
“Intelligence: An Art Show About Data Collection” by Sue Anne Rische opens in February.
PLANO, TX – January 2, 2020, / - Multimedia artist Sue Anne Rische announces the art exhibition “Intelligence: An Art Show About Data Collection” at The Arts Gallery in Plano, TX. The show will be on view from Wednesday, February 19 – Wednesday, March 18, 2020. An “Art Café” lecture will take place Thursday, March 5: 1-1:45pm with a closing reception later in the afternoon from 4-7pm.
Rische's installation, “Intelligence,” utilizes interactive technology to call attention to privacy and data collection. Viewers lose their connectivity once inside a centralized Faraday cage while a hidden message lurks on the walls. By encouraging the viewer to cage themselves in an effort to block all signals to and from their smart phone, Rische invites conceptual connections between information contained on your personal devices, imprisonment (willing or not), the lengths a person has to go through to protect themselves from corporate and government tracking, and the removal of oneself from participation in normal society. Rische pulls inspiration from Aldous Huxley's Brave New World and more recently Shoshana Zuboff's The Age of Surveillance Capitalism. Zuboff echos Huxley's concerns 87 years later as we voluntarily yield to “ignorance, learned helplessness, inattention, inconvenience, habituation, or drift.”
Sue Anne Rische lives and works in the Dallas–Fort Worth metroplex. She earned her Bachelor's Degree from Texas Tech University and her Master's Degree from the University of Washington and has shown in several countries including Japan, the Netherlands, Spain, and England. Sue Anne has been an art professor for over 24 years and teaches innovation in her foundational art classes. She has been actively creating and showing her privacy-based work for five years. More information can be found on her website: www.sueannerische.com.




 When I think about security and privacy, I often focus on sophisticated attacks and exotic exploits, or on user error and social engineering. A
When I think about security and privacy, I often focus on sophisticated attacks and exotic exploits, or on user error and social engineering. A  Let’s get this out right up front. I am a strong advocate for network neutrality.
Let’s get this out right up front. I am a strong advocate for network neutrality. David Shedd, former director of the Defense Intelligence Agency, recently published an OpEd on the damage that unrestricted focus on catching criminals can do to our general cyber security. It is great to see people with that kind of background speaking on on this critical issue.
David Shedd, former director of the Defense Intelligence Agency, recently published an OpEd on the damage that unrestricted focus on catching criminals can do to our general cyber security. It is great to see people with that kind of background speaking on on this critical issue.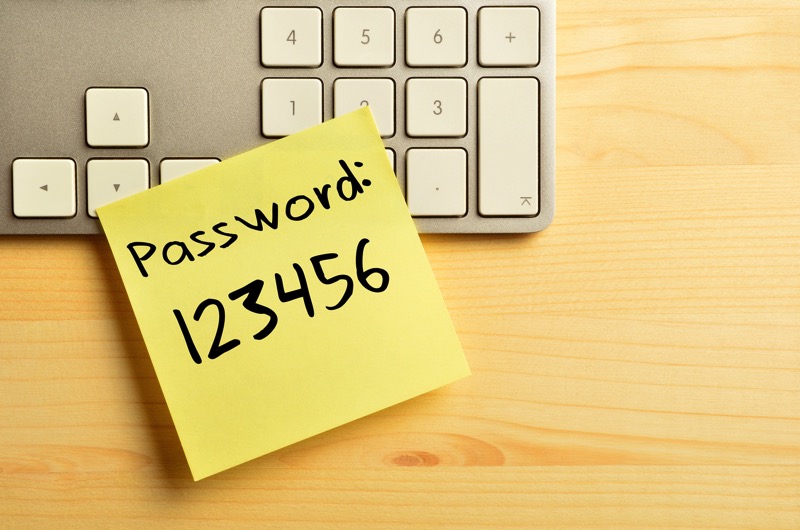 It is time to talk about passwords again. They are like the seatbelts of the security world. There are many more exciting security tools but few are as important to keeping you safe from the risks you encounter day to day.
It is time to talk about passwords again. They are like the seatbelts of the security world. There are many more exciting security tools but few are as important to keeping you safe from the risks you encounter day to day. Security firm
Security firm  On October 21st, a large number of websites, including some of the biggest names, were knocked off the Internet by a massive distributed denial-of-service (DDoS) attack. A DDoS attack occurs when thousands to millions of devices send traffic to a target, completely overloading its servers or Internet connection.
On October 21st, a large number of websites, including some of the biggest names, were knocked off the Internet by a massive distributed denial-of-service (DDoS) attack. A DDoS attack occurs when thousands to millions of devices send traffic to a target, completely overloading its servers or Internet connection.
 If you care at all about security and privacy, a recent security analysis of the D-Link DWR-932 B LTE router will make your head explode.
If you care at all about security and privacy, a recent security analysis of the D-Link DWR-932 B LTE router will make your head explode. Mac users have long had an unwarranted level of confidence about their immunity to malware and hackers. Palo Alto Networks’ recently discovered some Mac malware in the wild, which I hope will make us Mac users pay more attention to security. The malware, which targets mostly the aerospace industry, appears to be from an APT group they call “Fancy Bear”.
Mac users have long had an unwarranted level of confidence about their immunity to malware and hackers. Palo Alto Networks’ recently discovered some Mac malware in the wild, which I hope will make us Mac users pay more attention to security. The malware, which targets mostly the aerospace industry, appears to be from an APT group they call “Fancy Bear”. I had a great time talking with Gary about privacy, anonymity, security, Cypherpunks, WikiLeaks, and more. Check it out!
I had a great time talking with Gary about privacy, anonymity, security, Cypherpunks, WikiLeaks, and more. Check it out!


